A new kind of Android malware has hit the ranks these days. It allegedly integrates a banking trojan, a ransomware, and a keylogger. ThreatFabric security researchers have revealed that the malware packs all the three entities in one package. It is being called the MysteryBot Android malware.
MysteryBot Android Malware
At beginning upon discovery, the malware was alleged to be an updated version of LokiBot. Upon proper observation, it was observed that it wasn’t LokiBot as it comes with many new features. It is named as MysteryBot Android malware.
It has been found out that MysteryBot attacks handsets running Android 7x or Android 8x.
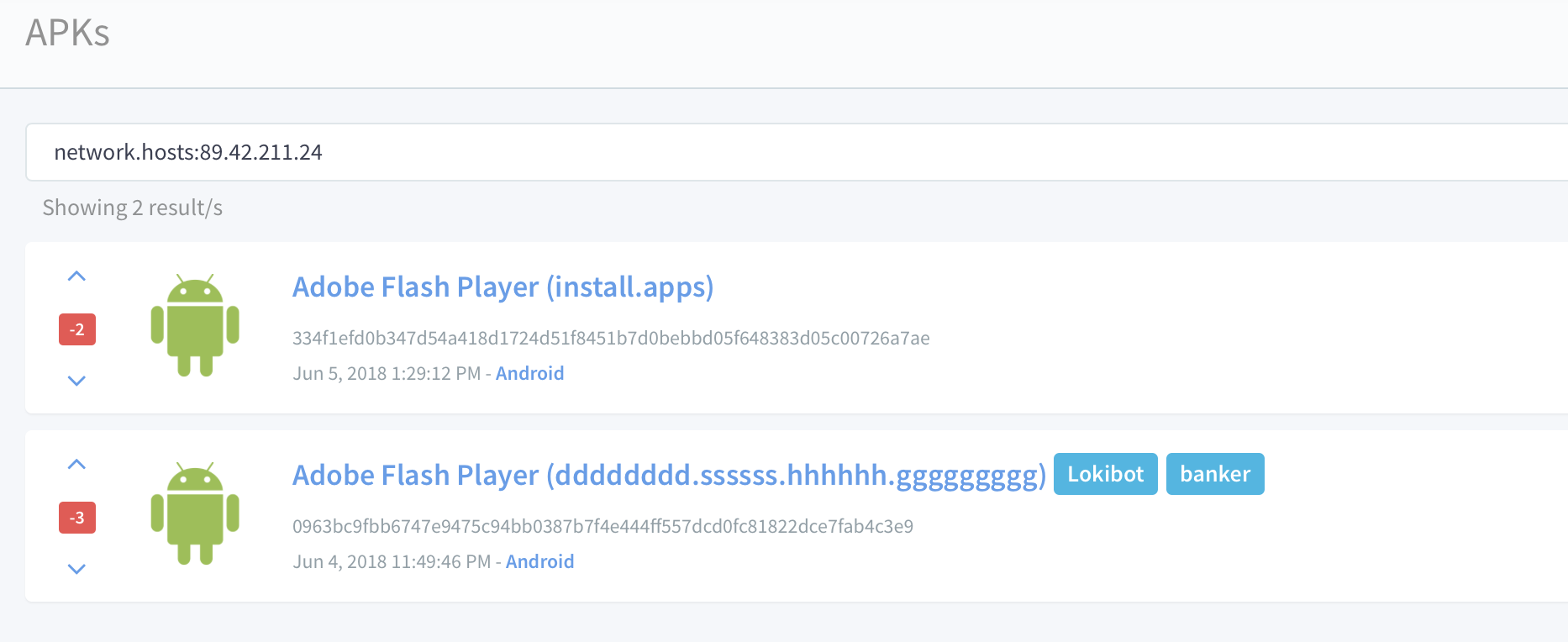
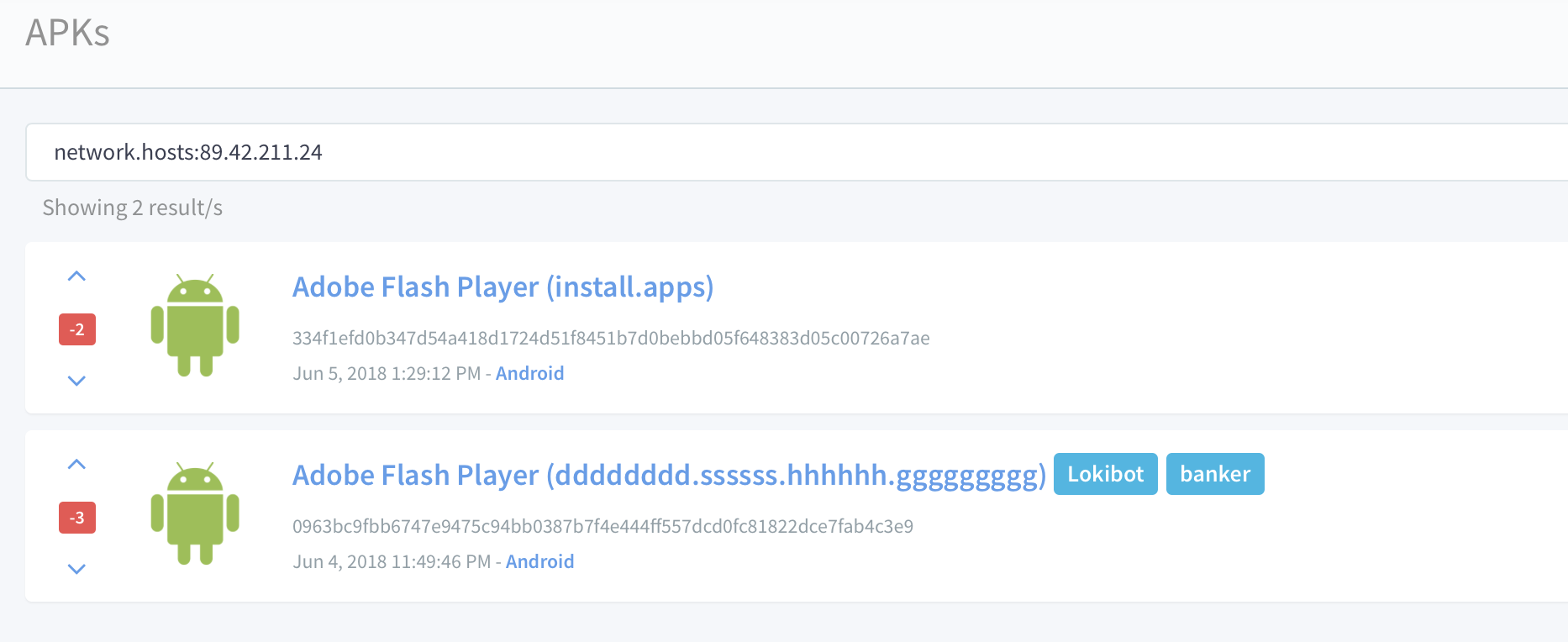
According to ThreatFabric, LokiBot and MysteryBot Android malware are “both running on the same C&C server.” As both share the same command and control server, it forms a strong link between both of them. There is a possibility that it has been made by the same creator.
MysteryBot Android malware can take control of a user’s handset. It also displays overlay, keylogging, and ransomware functionalities.
Also read – WhatsApp Windows App for Desktop Alleged To Be In Process
MysteryBot also can steal emails and start applications remotely. But it is still in development as it such tools are not active yet. It can even attack the devices with the latest Android versions– Nougat and Oreo. According to researchers, overlay screens are used by the malware. This makes it look like a real bank website. But it is actually run by attackers.
Package Usage Stats And Keylogger
According to the research team, a new method exploits a service permit called ‘Package Usage Stats’. It is accessible through the Accessibility Service permission in Android smartphones. It lets the malware enable and violate any other permission without the user’s permission.
The malware also consists of a keylogger. Researchers have mentioned that none of the known keylogging techniques was used. Rather, the MysteryBot Android malware calculates each row’s location and places a view over keys.
According to them, “This view has a width and height of zero pixels and due to the “FLAG_SECURE” setting used, the views are not visible in screenshots. Each view is then paired to a specific key in such a way that it can register the keys that have been pressed which are then saved for further use”.
They also mentioned, “The code for this the keylogger seems to still be under development as there is no method yet to send the logs to the C2 server.”
“The encryption process puts each file in an individual ZIP archive that is password protected, the password is the same for all ZIP archives and is generated during runtime. When the encryption process is completed, the user is greeted with a dialog accusing the victim of having watched pornographic material,” said researchers.