Cupertino-based tech giant Apple has received a problem to solve now after a claim by cybersecurity company Wandera that the Siri Suggestions feature can easily be misused for phishing attempts in the foreseeable future.
Siri Suggestions Feature Exploitation
According to the cybersecurity company, phishers can use Siri’s ‘Maybe’ feature to mislead users as who they really are. So basically when a number is not known, Siri usually tries to find suggestions by ‘Maybe: XXXX’ banner on the incoming call screen or iMessages.
A Fortune report elucidates that there are two ways to do this. Misusers can create a fake account which will come in the Siri Suggestions feature. Then an email will be sent to the target. If the target responds then the ‘Maybe’ feature shows the fake account name whenever the phisher calls or texts. The report mentions that “There are two ways to pull off this social engineering trick… The first involves an attacker sending someone a spoofed email from a fake or impersonated account, like “Acme Financial.” This note must include a phone number; say, in the signature of the email. If the target responds-even with an automatic, out-of-office reply-then that contact should appear as “Maybe: Acme Financial” whenever the fraudster texts or calls next”.
Also read – Apple watchOS 5 Equipped With Parkinson’s Disease Tracking API
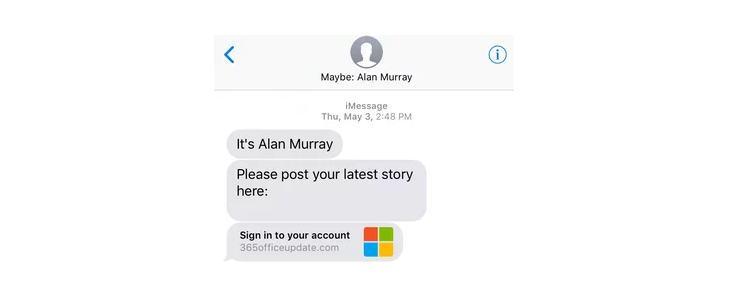
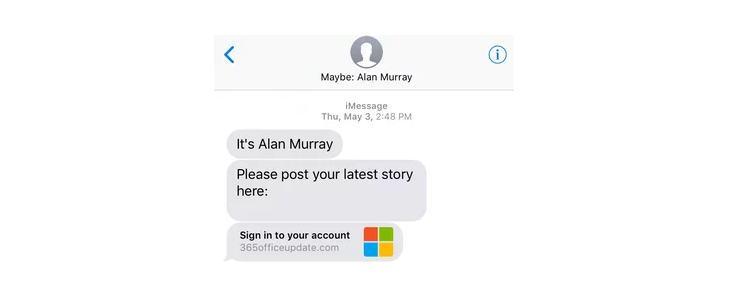
The alternate method is through text messaging. The report states that “The subterfuge is even simpler via text messaging. If an unknown entity identifies itself as Some Proper Noun in an iMessage, then the iPhone’s suggested contacts feature should show the entity as Maybe: [Whoever]”.
Interesting take. Really think this is a complete non-issue however. Has been an iOS feature since 2015. Apple could probably easily add a switch to disable it though. https://t.co/zGfaVrfkgx
— Mark Gurman (@markgurman) June 11, 2018
Bloomberg’s Mark Gurman has tweeted that Siri Suggestions has been there since 2015. , Apple could easily add a switch to toggle the Siri feature off. Wandera said it reported this issue to Apple which noted it as a software issue, and not a security vulnerability.
For more information, click here.